Blog
U.S. Thieves Exploring ATM Jackpotting Attacks
In January, the Secret Service warned U.S. banks that a form of robbery known as ATM jackpotting, which had already proliferated across Europe, Asia, and Latin America since as early as 2009, had finally made its way to the U.S., with at least six attacks taking place within a single week.

In January, the Secret Service warned U.S. banks that a form of robbery known as ATM jackpotting, which had already proliferated across Europe, Asia, and Latin America since as early as 2009, had finally made its way to the U.S., with at least six attacks taking place within a single week.
The underlying factors contributing to the emergence of ATM jackpotting in the U.S. are not entirely clear. However, Flashpoint analysts believe U.S. companies’ ongoing adoption of the same EMV security standards that have made payment card fraud infeasible in other countries is driving threat actors to explore other types of crime. It also appears as though actors from other countries are bringing their tactics, techniques, and procedures to the U.S., or at least sharing them with U.S.-based threat actors, as evidenced by the use of Ploutus.D malware, which was first observed in Mexico in 2013.
ATM Jackpotting: An Overview
Also known as logical attacks, ATM jackpotting attacks are defined as manipulation of an ATM that causes it to eject cash, either by infecting it with malware or connecting it to an external device, referred to as a “black box,” which connects to the machine’s cash dispenser as a stand-in for the ATM’s CPU. If the ATM’s security controls are bypassed successfully, the black box can receive commands from another device, prompting the machine to dispense cash.
Flashpoint analysts observed very little chatter about black-box attacks that could possibly be linked to actors residing or operating in North America. However, in May 2017, Europol published a press release announcing the arrests of 27 individuals associated with black-box attacks across Europe, more specifically, Czech Republic, Estonia, France, the Netherlands, Romania, Spain, and Norway.
In Europe, the total number of ATM jackpotting attacks increased 231 percent from 58 incidents in 2016 to 192 in 2017. Flashpoint analysts believe ATM jackpotting is also widespread in parts of Asia and Latin America, but precise numbers are not available.
ATM jackpotting typically requires some form of physical connection to the targeted machine, typically through its USB port. In some cases, standalone ATM operators with lax security practices have been known to use generic ATM keys, which Flashpoint analysts have observed for sale on legitimate, open-web ecommerce sites. However, in most cases, threat actors must gain access to ATM ports through other means, such as drilling holes in, or melting, its plastic shell. Jackpotting crews have also been known to use endoscopes to reconnoiter the machine’s internal systems.
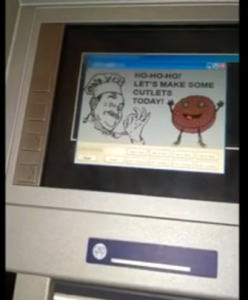
Numerous malware families available on DDW forums and marketplaces have been known to be utilized in jackpotting schemes, including the Ploutus malware family, which first appeared in 2013 but remains under active development, and Cutlet Maker, which Flashpoint analysts first observed for sale on DDW forums in June 2017.

The Role of the Deep & Dark Web
Flashpoint analysts have observed widespread discussion of ATM jackpotting attacks on the DDW, typically involving the use of malware such as Ploutus.D, Cutlet Maker, Ripper, and Tyupkin. Flashpoint analysts have also observed threat actors exchanging instructional guides on how to target specific types of machines using specific malware strains, thus lowering the barriers to entry for carrying out ATM jackpotting attacks among low-skill threat actors.
Cybercrime forums provide threat actors interested in ATM jackpotting with a platform to connect with other criminals and hatch schemes. For example, in March 2017, an actor on a Russian-language forum posted in English, claiming to have full USB access to a certain type of ATM and stating that they were seeking a partner with access to ATM malware.
These partnerships may transcend geographic boundaries, as evidenced by multiple posts on a Russian-language DDW forums seeking accomplices in a scheme targeting ATMs in Asia in mid-to-late 2017. The actors did not elaborate on the reasons for their focus on Asia or their avoidance of the U.S. However, Flashpoint analysts speculate that these actors are likely attempting to take advantage of the potentially lax security measures they expect to find in certain regions with less-developed cyber defenses.
ATM Jackpotting Attack Execution
Flashpoint analysts believe criminals may leverage ATM technical support manuals not intended for public consumption that have been leaked online to obtain the specific information needed to plan a jackpotting attack.
According to one tutorial on an English-language DDW forum, the initial visit to a target ATM to inject malware or bypass security controls should only take two or three minutes, with a maximum duration of four minutes. In order to execute a technical attack in such a small window of time, jackpotting crews must proactively determine the ATM vulnerabilities they intend to exploit, as well as the location and means of getting to access points such as USB ports, often using a drill and/or endoscope. Jackpotting crews may also be able to determine when the ATM’s cash box is filled, as well as any daily limits for dispensing cash, in order to maximize the amount of cash they are able to steal.
Once they have selected a machine to target, ATM jackpotting crews—typically disguised as ATM technicians to evade suspicion—physically tamper with the ATM to either infect the it with malware or bypass its security controls and connect it to an external device.
Some ATM jackpotting crews prefer to execute their attacks in one visit, cashing out the machine immediately after injecting it with malware or connecting it to an external device. Others find a multi-visit approach to be more inconspicuous, deploying mules to retrieve the dispensed funds after the actors disguised as ATM technicians have finished servicing the machine. After the mules have carried out their heist, the “ATM technicians” return to the machine to return it to its pre-attack state and retrieve any hardware connected to the ATM.
Mitigation Measures
To combat ATM jackpotting, Diebold Nixdorf advises ATM operators to limit physical access to ATMs using appropriate locking mechanisms and two-factor authentication. ATM operators should also keep firmware updated with the latest security functionality, use secure encryption, and immediately investigate any suspicious activity.
Assessment
Given the lucrative nature of ATM jackpotting attacks, Flashpoint analysts believe threat actors will continue to target standalone ATMs perceived to be outdated, unpatched, or otherwise vulnerable. Although there has been a recent wave of jackpotting attacks in the U.S., Flashpoint analysts do not believe the attacks will become as pervasive as they are in certain areas of Asia, Eastern Europe, and Latin America where outdated but still operational ATMs are more commonplace.
Block has been deleted or is unavailable.

