Blog
Top 10 Ransomware Trends: Board Responsibilities, Tracking Ransomware, and Mitigating Risk
From summer 2021 to early 2022, the ransomware ecosystem changed from high-profile, high-impact, big-game hunting activity to a period of relative quiet characterized by mid-level targets, higher ransom demands, and the first hacktivist ransomware attack on critical infrastructure.

From summer 2021 to early 2022, the ransomware ecosystem changed from high-profile, high-impact, big-game hunting activity to a period of relative quiet characterized by mid-level targets, higher ransom demands, and the first hacktivist ransomware attack on critical infrastructure.
The ecosystem shift is primarily the result of three factors: the international notoriety of certain 2021 attacks (particularly Colonial Pipeline), subsequent law enforcement action (particularly the arrests of “REvil” members), and increased organizational and company security measures. Nevertheless, ransomware remains an active and lucrative venture, meaning that ransomware activity can be expected to continue through 2022, albeit at potentially different levels and with different tactics, techniques, and procedures (TTPs).
Here are 10 ransomware trends—from liability and insurance considerations to compliance issues, fiduciary duties, and cybersecurity measures—that boards should pay close attention to.
1) Ransomware targets will expand
Data for the ransomware landscape in 2021 showed a more diverse range of industries targeted by threat actors, in addition to a rise in the total number of organizations impacted. Over 4,000 companies were identified as having been breached last year, not including the many others that submitted to ransomers’ demands without publicization, which make this figure higher.
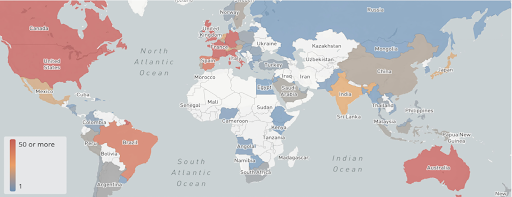
Organizations in the United States, Canada, and Europe were most affected by ransomware, while critical infrastructure, health care, and government were among the wide range of industries attacked. As the ransomware landscape grows, it’s likely that the range of targets will grow with it.
2) Threat actors will use several routes to successfully attack
2021 saw an increase in the severity of attacks on a technical level, with threat actors evolving from reliance on permanent data encryption to more aggressive methods. As tactics develop, it’s likely that ransomware attacks will consist of more components to increase the odds that the ransom will be paid. New methods include:
- Coordinating ransomware attacks with major corporate events, like IPOs and M&A activity, to increase pressure on victim
- Sharing victim’s names and confidential business data on victim-shaming sites
- Hosting data sell-off auctions, which allow outside parties to also bid on victims’ data
- Reaching out to media outlets and/or concerned stakeholders to publicize the attack and remove the opportunity for privacy
3) Liability risk for organizations will grow
With the increase in both the quantity and severity of ransomware attacks, the bodies that safeguard organizations in the event of a breach are struggling to keep up. Regulators, insurers, and stockholders are all experiencing the weight of 2021’s ransomware trends, which means that organizations should prepare for less support—and therefore, even more focus on strong prevention tactics.
4) Cyber insurance will not provide the protection it once did
Ransomware accounted for 75 percent of all claims against cyber insurance policies in 2021, up from 55 percent in 2016, showing a significant rise in its impact on insurance providers. In turn, premiums have seen annual increases of over 25 percent, while loss ratios are up 50 percent year-over-year.
The rapid boost in volume, pace, and cost of ransomware attacks has made it unsustainable for insurers to provide the same safety net they once did for organizations. As a result, insurance providers may follow AXA’s lead and revise policies to exclude ransomware payment reimbursement, which was implemented by the French insurance company in 2021. Boards should consider this as they plan their own insurance positioning and cyber defense expenditures in 2022.
5) Paying ransom may become impermissible under sanctions compliance law
The Office of Foreign Assets Control (OFAC) tried to slow the growth of criminal digital finance infrastructure in 2021 by discouraging private companies and citizens from paying ransom and extortion demands. Instead, they emphasized having strong defense measures to minimize the risk of a successful ransomware attack.
Before paying ransom, organizations must run OFAC and sanctions compliance checks to confirm the permissibility of sending payment under the law. This will lead to longer periods of time between attack, payment, and subsequent recovery, and will limit the types of events where payment is legally permissible.
In light of this, directors should prioritize thorough understanding of OFAC guidance, and should ensure that compliance leaders incorporate this guidance into the organization’s cyber risk preparedness plan in 2022.
6) Public disclosure requirements will expand in 2022
Ransomware attack disclosure is presently not required by the U.S. Security and Exchange Commission (SEC) unless the attack meets a certain materiality threshold. However, the SEC is more closely scrutinizing disclosures, and holding victim organizations that choose not to disclose ransomware attacks, to a higher standard. Both federal regulators and individual states are considering laws that would require the public disclosure of ransomware events, although Flashpoint does currently view this as an imminent possibility.
Nevertheless, heightened attention on the part of regulating bodies to ransomware attacks and their subsequent public disclosure (or lack of) means that directors and legal teams should carefully monitor requirements. Public disclosure of attacks and ransom payments can significantly impact customer confidence, third-party relationships, and stock price, which makes the potential for obligatory disclosure especially important as organizations map out their prevention and defense protocols.
7) Directors will be held to a higher fiduciary standard
2021 trends have indicated that the fiduciary duties of directors during ransomware attacks will grow, holding them to a stricter level of responsibility in the event of a breach. For example, Delaware courts have recently continued the expansion of directors’ obligations related to both ransomware attacks and cybersecurity attacks overall, validating in a recent case that directors have a responsibility to oversee cybersecurity in response to a large data breach claim from Marriott in October 2021 (Fire Ret. Sys. of St. Louis v. Sorenson, et al., (Del. Ch. Oct. 5, 2021)).
8) Boards must proactively oversee cybersecurity measures
Trends related to the specifics of ransomware attacks have provided boards with clear action items as they consider how to best support their organizations in preventing breaches. Namely, they should concern themselves with the following areas of their companies’ prevention and mitigation plans:
- Defend: Ensure companies are prepared to defend through investment in cybersecurity infrastructure, inclusion of cybersecurity in organization’s overall risk management framework, empowerment of security teams in the form of budget and autonomy, and the compulsion of security best practices.
- Prepare: Prime organization to attack quickly and effectively in the event of an attack, which includes regular review of the organization’s incident response plan and knowledge of which data is most valuable to a company’s operations, and what the monetary cost would be of its loss and recovery.
- Respond: Validate the careful and legal execution of attack response according to the predetermined plan.
9) Directors and boards will be called on to provide oversight during an attack
To ensure best practices are used during an attack, leaders will be responsible for promoting emotion-free execution of the incident response plan and positioning the organization for the best possible outcome. Especially important is confirmation that the company is complying with legal requirements, including OFAC and sanctions laws, and that the communication plans are followed so that all involved parties have their needs met.
10) Prevention is key
Given the enhanced abilities of threat actors and the tightening of disclosure and payment compliance requirements that will likely highlight 2022, directors should focus on the prevention of attacks as their main objective. Severity of the attacks coupled with significant negative consequences in the event of a public breach disclosure limit the guaranteed effectiveness of any response method.
Instead, increased investment in prevention infrastructure, which includes broader cybersecurity infrastructure and general adoption of security best practices among all employees, will differentiate between companies that are able to preserve their critical data and companies that will need to deal with long lasting consequences of a breach.
This blog has been adapted from Flashpoint President Donald Saelinger’s article, “Board Responsibilities for Mitigating Ransomware Risk in 2022,” which originally appeared in the National Association of Corporate Directors (NACD) 2022 Governance Outlook. To download that report, click here.


