Blog
This Is What COVID Fraud Looks Like
Over the course of the COVID-19 pandemic, threat actors have leveraged fear, uncertainty, and doubt to turn a profit. Their fraud schemes target government relief funding; they advertise fake treatments or cures; and, lately, they buy, sell, and trade fake (negative) test results or proof of vaccination.
COVID Fraud Timeline: Tests, Treatments, and Vaccines
Over the course of the COVID-19 pandemic, threat actors have leveraged fear, uncertainty, and doubt to turn a profit. Their fraud schemes target government relief funding; they advertise fake treatments or cures; and, lately, they buy, sell, and trade fake (negative) test results or proof of vaccination.
In late 2020, prior to the release of a successful vaccine, most chatter about fake documentation on illicit forums was related to the falsification of test results.
Flashpoint analysts also observed some chatter, particularly within online conspiracy theory communities, about the inevitability of worldwide vaccine requirements and health passports, as well as speculation about how to obtain fake vaccination cards, thereby resisting forthcoming vaccinations.
Below is a screenshot from Dread, an underground social news and discussion website, about a method to falsify test results.

- When the vaccine rollout began in many countries in early 2021, chatter about fraudulent documentation associated with COVID-19 testing increased. Around this time, threat actors were buying, selling, and trading tips on how to best falsify vaccination documentation. Flashpoint analysts have already observed instances where threat actors share: vaccine card templates; tips on how to obtain legitimate details—including PII, dosage info (lot numbers, e.g.), vaccine dates, site, and type—to put on vaccine cards; and claims of insider access to obtain legitimate vaccination record details to repurpose on forged cards
Examples of COVID Fraud
Flashpoint analysts identified numerous occasions where actors also shared links to templates on websites hosted by state-run departments of health, which were freely accessible and able to be downloaded and manipulated.
Although threat actors did not always express specific reasons as to why they were seeking falsified documentation, Flashpoint analysts note that many of these conversations occurred in communities dedicated to far-right conspiracy theories and domestic extremism, particularly on Telegram, an encrypted messaging service.
Below is an image of a link to a COVID-19 vaccination card template hosted on Wyoming’s Department of Health website that was shared in a Telegram community, along with instructions for how to fill it out with fake information.

An English-speaking threat actor on Dread created a thread where they asked other users how to obtain a falsified negative COVID-19 test, which they need due to current travel requirements.
A separate threat actor replied that the user should private message them, because they have access to a template that they used to create a positive COVID-19 test. They claimed to have used this template for five months to get off of parole and avoid drug testing and check-in requirements—and that they have successfully created fictitious test results for other friends as well.
Related Reading: Counterfeit COVID Vaccine Card Market Takes Hold in the U.S. and Europe
An English-speaking threat actor posted that they were looking for someone to manufacture a forged negative COVID-19 test. They explained that they had planned to travel to a state requiring a negative test, but did not have time to legitimately obtain a negative test. They offered to provide an old negative test of theirs to someone who may be willing to alter the dates to reflect a date within the needed time frame.
In the spring and summer of 2021, some organizations returned to in-person operations along with governments, which similarly relaxed foreign travel and border restrictions. During that time, some threat actors specifically advertised or sought out falsified documents (including false negative tests or fake proof of vaccination) to facilitate travel or to provide proof to their employer. Flashpoint analysts observed buying and selling of vaccine cards in a variety of countries and languages.
An English-speaking threat actor operating on Telegram channel advertised their service selling forged COVID vaccination cards that they claim are fully registered online.
An English-speaking vendor posted on a dark web marketplace that they were selling a “full Irish vaccine passport.” In the description, they noted that this offering included notations for two vaccine doses, including batch numbers, although they did not indicate which vaccine would be indicated on the document. They also claimed that this would allow buyers to travel without taking COVID tests.
An English-speaking threat actor posted on Telegram advertising their services producing forged vaccine certificates, cards, and passports. The threat actor claimed that their documents allowed users to travel anywhere they wanted to, and included an image of a forged vaccine card from the UK.
Related Reading: Cybercriminals Salivating over Access to New Coronavirus Stimulus Funds
A French-speaking threat actor initiated a thread on Dread where they were seeking to acquire a French COVID vaccination passport or equivalent documentation.
An English-speaking vendor posted an advertisement on a dark web marketplace for a National Health Service (NHS) vaccine card for US$25. They indicated in the advertisement that they were willing to ship worldwide, and that they could provide both blank and “registered” cards (which likely contain vaccination record details).
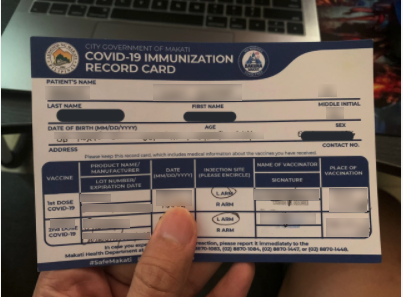
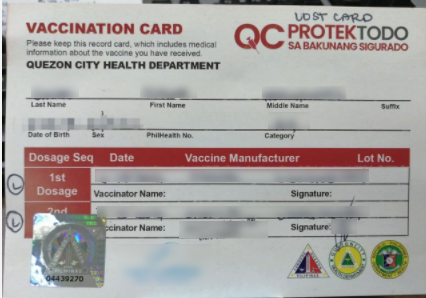
On July 16, a Chinese-speaking threat actor posted on a Telegram channel where they advertised the sale of forged vaccination cards for various cities in the Philippines.
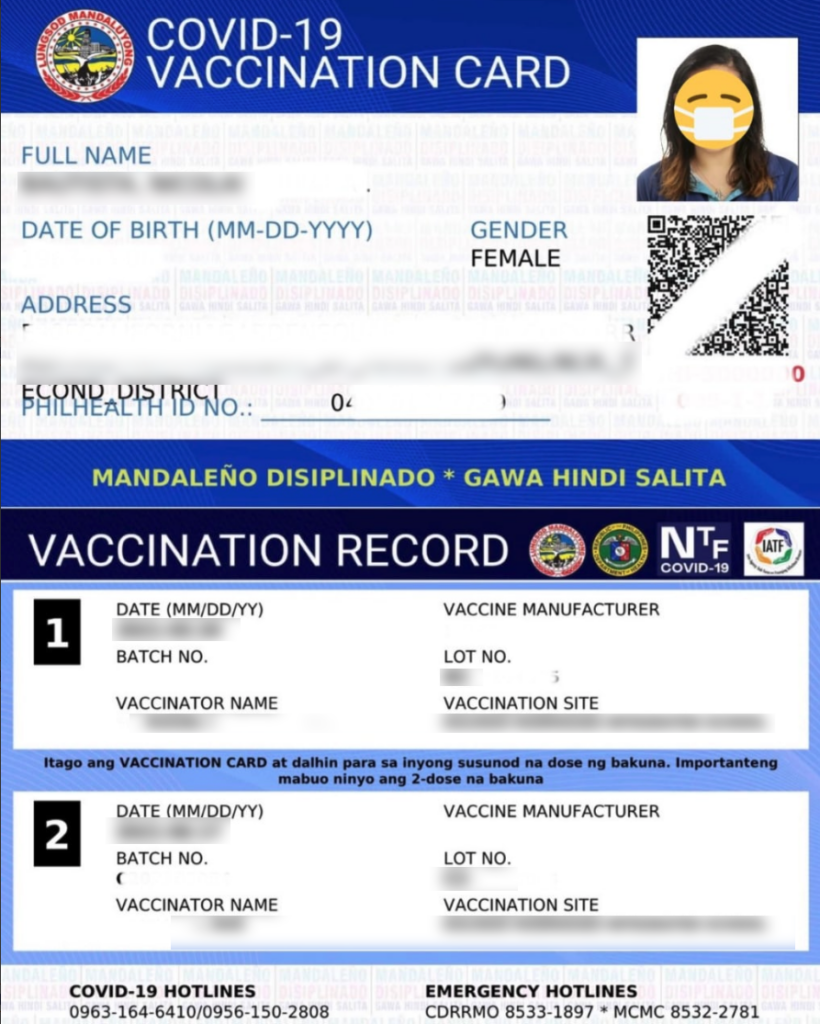
Although implementation of electronic vaccine cards is limited (particularly for individuals traveling to foreign countries), Flashpoint analysts have observed some threat actors seeking to circumvent security controls in their home countries where electronic vaccination and contact tracing databases are used.
An actor on Dread wrote a post asking for help submitting false information to the NHS databases claiming they had been vaccinated. They were also interested in buying a forged UK vaccine passport.
![]()
Another actor on Dread expressed opposition to databases containing personally identifiable information linked to vaccination records, and solicited advice for how to falsify QR codes generated to verify vaccination status on CoronaCheckApp, used in the Netherlands.
- An actor posted in a Telegram channel with an image of a reference form from the NHS verifying COVID vaccination status. They claimed in a follow-up post that they had a JPEG file for the document that they were willing to share and also claimed to have an EU vaccination certificate template they could share as well. The threat actor claimed that the NHS form is currently the “holy grail” for individuals seeking to travel.

- In a German-language Telegram channel, a threat actor advertised the sale of proof of vaccination along with a corresponding QR code. The threat actor noted that they were expressly selling these to individuals who did not want to get vaccinated but wanted to have proof of vaccination.

- Another threat actor operating on Telegram attempted to appeal to individuals who believe the vaccine is unsafe in their advertisement. They claimed to be able to sell vaccination records and accompanying QR codes to individuals who needed to provide proof of vaccination.

As governments and private sector firms are adding additional requirements for COVID-19 vaccination status, actors are likely to continue looking to illicit sources to acquire fake documentation to avoid obtaining a vaccine. Threat actors may also continue to find ways to acquire falsified test results since in many cases that remains an alternative to providing proof of vaccination status.
Related Reading: COVID-Related Cybercrime Swells in 2021: Stimulus Fraud, Vaccine Scams, and Disinformation All Front and Center
Additionally, analysts anticipate that governments and private sector companies will continue to evaluate and implement electronic solutions for customers and citizens to provide proof of vaccination. As a result, threat actors across illicit communities are likely to increasingly discuss methods to defeat those security controls and falsify documentation due to privacy concerns or anti-vaxx positions.
The Impact of COVID Fraud
The black market for fraudulent proof of vaccination could have a significant impact on public health. When individuals illegally misrepresent their health status with forged documentation, they may contribute to the continued spread of COVID-19 and its variants, thereby prolonging the pandemic’s grip on societies worldwide.
Additionally, as employers implement vaccination requirements, threat actors seeking to use falsified documentation may attempt to use fake records to satisfy employer rules, introducing additional risks to organizations seeking to return to in-person operations. The demand for forged vaccination documentation may also represent an appeal for rogue insiders to exploit privileged access to vaccination patient information for malicious purposes.
Related Reading: Considerations for Updating Near-Term Intelligence Requirements in Response to COVID-19

