Blog
Necurs Rootkit Spam Continues Proliferating Dating Scam
The recent arrest of prolific spammer Petr Levashov left a void in the spamming community that some actors appear to be seeking to fill by launching large-scale spam campaigns — some of which are fueled by Crimeware-as-a-Service (CaaS) offerings. One such campaign linked to online dating scams has proven to be especially damaging because it is powered by Necurs — the largest spam botnet in the world.

The recent arrest of prolific spammer Petr Levashov left a void in the spamming community that some actors appear to be seeking to fill by launching large-scale spam campaigns — some of which are fueled by Crimeware-as-a-Service (CaaS) offerings. One such campaign linked to online dating scams has proven to be especially damaging because it is powered by Necurs — the largest spam botnet in the world.
Background
Necurs first emerged in 2012 and has since become notorious for fueling large-scale email campaigns that distribute malware (particularly Locky ransomware, the Dridex banking trojan, and most recently, Jaff ransomware), propagate “pump-and-dump” fraud schemes, and/or bait recipients into purchasing scam memberships for disreputable dating websites.
Known to have been distributed by the Neutrino Exploit Kit, Necurs is arguably one of the most prolific Windows OS rootkits that loads modules for CaaS offerings. Indeed, the Necurs administrator has been known to rent out the botnet infrastructure to various top-tier cybercriminals seeking to distribute spam. However, as the Necurs source code and its ownership remain closely-guarded by the administrator, the service is typically only available to heavily-vetted elite cybercriminals.
Dating Affiliate Scams
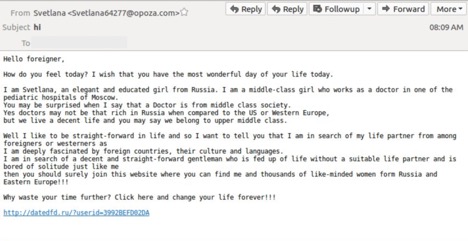
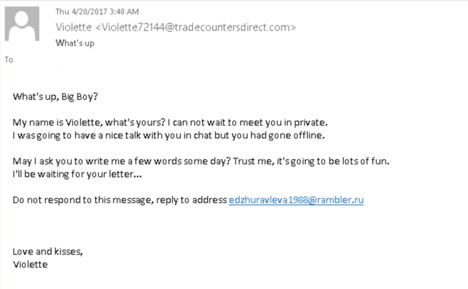
Dating affiliate scams are an extremely common spam tactic that enables cybercriminals to steal money from unsuspecting individuals by luring them into fake dating websites. In such scams, cybercriminals typically create fake dating profiles pretending to be, for example, an attractive woman residing in one of the former USSR countries. The goal is to entice a Western admirer to initiate contact and eventually become enamored with the woman represented in the fake profile. After some time, when the potential victim appears to be fully convinced of a fledgling romance and considering a real-life meeting, he will be asked to transfer money to cover travel and visa expenditures. Once the money is sent, the fraudster ceases all contact and absconds with the funds, subsequently repeating the scheme with a new victim.
In mid-April 2017, one particular Necurs botnet associated with Domain Generation (DGA) seed “5” began distributing dating affiliate scam emails. Also referred to as “lures,” these emails prompt the user to complete a registration form, after which point they receive information from USSR-Star[.]com, a Russian dating website known to target men in the Western Hemisphere seeking companionship. Indeed, this specific dating site has a history of using fake profiles to entice men into buying dating subscriptions.
In addition to the financial and often emotional hardship these dating scams can inflict on their victims, scams powered by the Necurs botnet can be especially damaging. Not only are Necurs malware infections extremely difficult to detect, but infected devices may face compromised security, information theft, and/or become more vulnerable to other types of malware infections.

Once infected with Necurs malware, machine statistics are reported to the spambot panel, which includes the following fields:
• Online
• HasAdmin
• Rootkits
• NoNAT
• Unactivated
• Blocked
• Total 24h
• Deleted_Lang
• Deleted_GeoIP
• Installs (ALL)
• Installs (ID)
• Traffic_IN
• Traffic_OUT
Mitigation Recommendations
Above all else, it is crucial to recognize that dating affiliate scams and other spam campaigns fueled by the Necurs botnet present a high potential for damaging consequences. As such, organizations and individuals alike should strongly consider the following recommended mitigation tactics in order to help reduce their risk:
• Block and restrict possible network activities associated with the Necurs dating affiliate domains (listed below).
• Never loan money nor give out personal information to anyone whom you have not met in-person
• Use only trusted, well-known online dating sites
Indicators of compromise (IOCs) are associated with the following domains:
• datedfd[.]ru
• datedfu[.]ru
• datedgg[.]ru
• dateghh[.]ru
• dategtt[.]ru
• datehgg[.]ru
• dateioo[.]ru
• datejhg[.]ru
• datekll[.]ru
• datelkk[.]ru
• dateoii[.]ru
• datersf[.]ru
• datetgg[.]ru
• dateuii[.]ru
• dateuns[.]ru
• dateffo[.]ru
• dateffk[.]ru
• dateffp[.]ru
• datingmarm[.]ru
• marmdating[.]ru

