Blog
“Necurs” Botnet Fuels Massive Spam Campaigns Spreading “Jaff” Ransomware
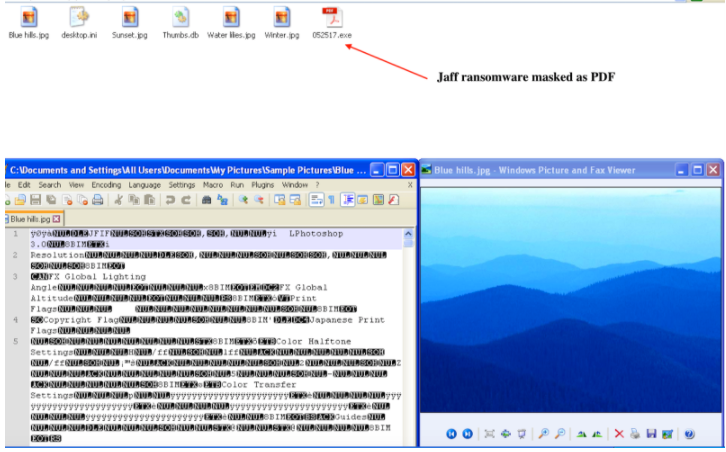
Starting on May 11, 2017, Flashpoint analysts observed several large spam campaigns originating from the Necurs botnet that aim to dupe recipients into opening malicious attachments that infect their computers with “Jaff” ransomware. These spam campaigns feature a multi-stage infection chain including a PDF file, a malicious Microsoft Office document, and finally, the Jaff ransomware loader. This same infection chain has been utilized in the past to infect computers with the Dridex banking Trojan and Jaff’s predecessor, Locky ransomware.

Starting on May 11, 2017, Flashpoint analysts observed several large spam campaigns originating from the Necurs botnet that aim to dupe recipients into opening malicious attachments that infect their computers with “Jaff” ransomware. These spam campaigns feature a multi-stage infection chain including a PDF file, a malicious Microsoft Office document, and finally, the Jaff ransomware loader. This same infection chain has been utilized in the past to infect computers with the Dridex banking Trojan and Jaff’s predecessor, Locky ransomware.
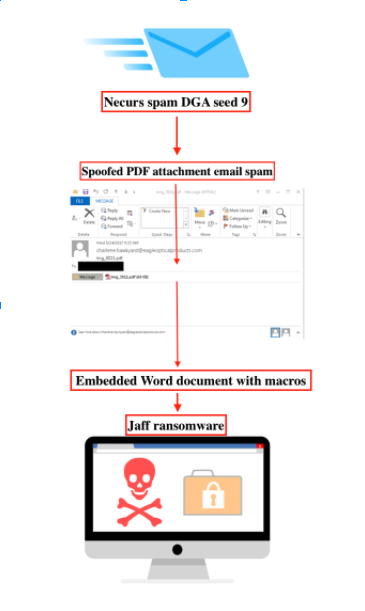
The Necurs botnet is comprised of smaller “sub-botnets” distinguishable by the seed value used in the malware’s code for domain generation algorithm (DGA). Although these sub-botnets send different kinds of spam when compared to one another, they all share the same command-and-control (C2) infrastructure. Flashpoint has thus far observed Jaff ransomware emanate from the spam module with a DGA seed of nine.
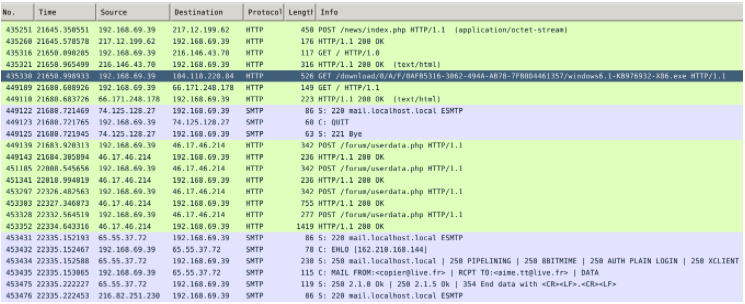
Prior to a spam run, the node infected with the Necurs malware will first perform a series of checks to ensure it is capable of sending spam. The infected node first receives an updated list of C2 IP addresses for the spam module before it verifies Internet connectivity by downloading Service Pack 1 for Windows 7. Once these checks pass, the bot will do a final connectivity check for Simple Mail Transfer Protocol (SMTP; TCP Port 25) as depicted in the following packet capture:
Ransomware Analysis
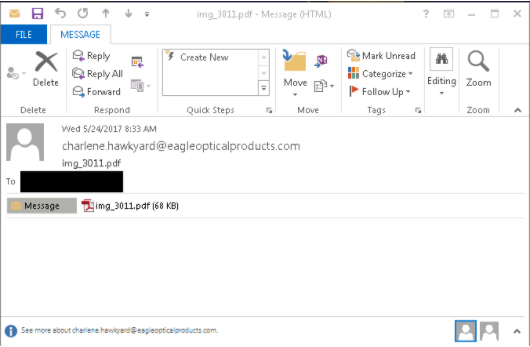
The spam attachments are PDF files containing JavaScript code that automatically executes upon opening the file via the “OpenAction” function. This JavaScript code extracts an embedded, malicious Office document from an object section of the PDF file.
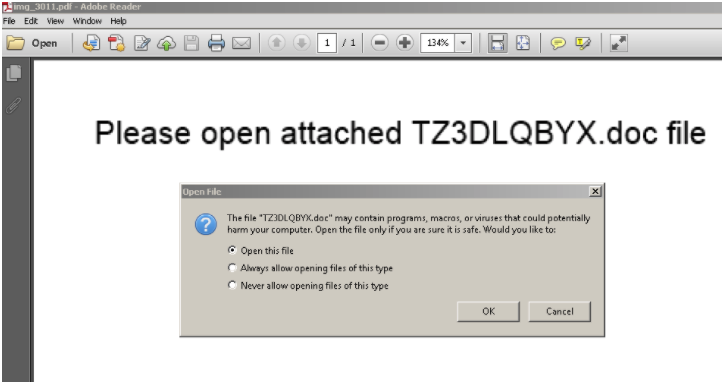
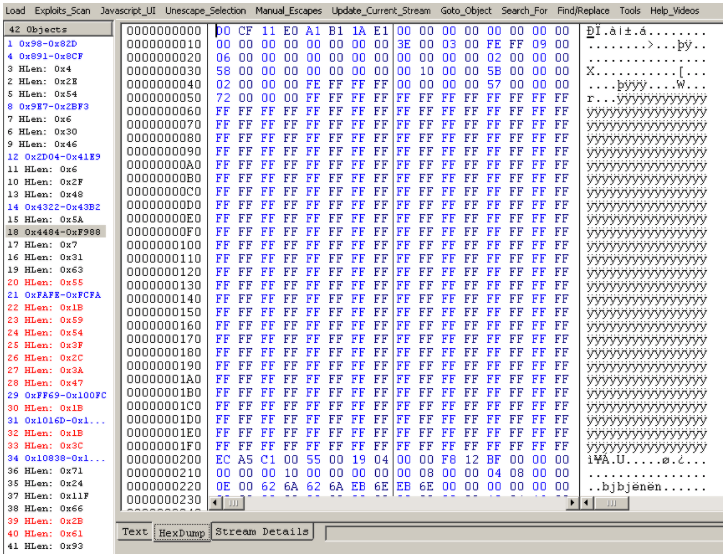
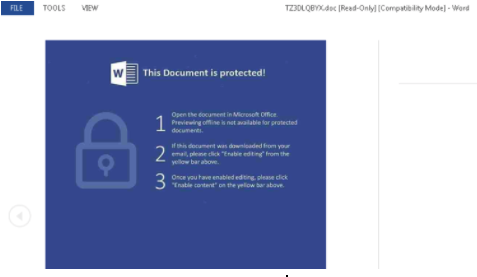
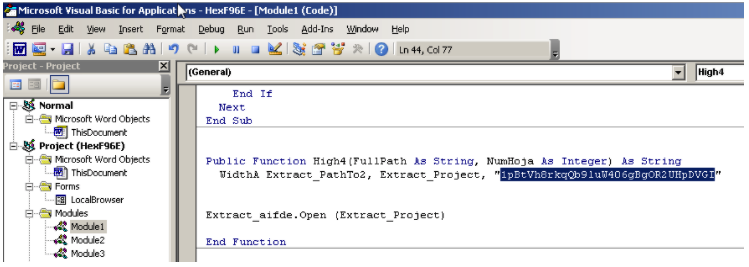
The next item in the infection chain is the malicious Microsoft Office Document that is opened via JavaScript code from the PDF file. This Word document contains macros that download an encrypted binary from one of four URLs, decrypts it with a hardcoded XOR key, then executes the binary – the Jaff ransomware loader.
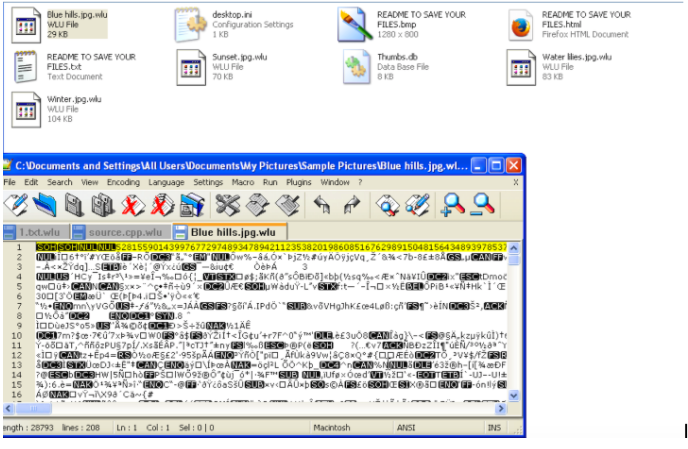
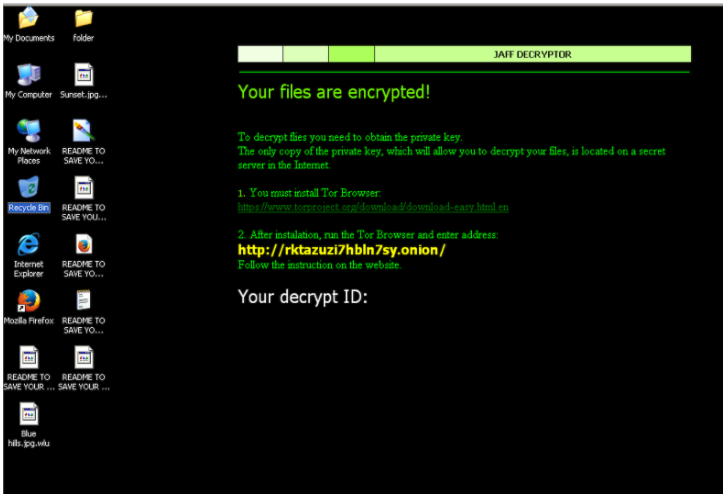
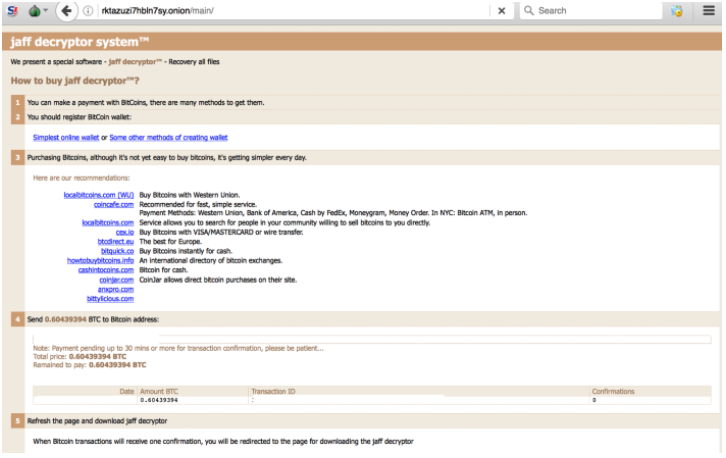
The Jaff ransomware is a 32-bit Windows executable, containing the malicious obfuscated code. Jaff explicitly targets Windows systems, enumerating the targets’ local file system by searching for specific file extensions to encrypt. Files that have been encrypted are renamed appending the extension .wlu or .jaff. Such extensions are typical for this ransomware. The victim obtains a unique Jaff ID on the Tor website.
The Jaff ransomware sets encryption messages localized to the language detected in the system. Just like its previous variant Locky, this ransomware renders and saves bitmap files in each directory with the encrypted files. The bitmap file is used as a wallpaper displaying the ransom message.
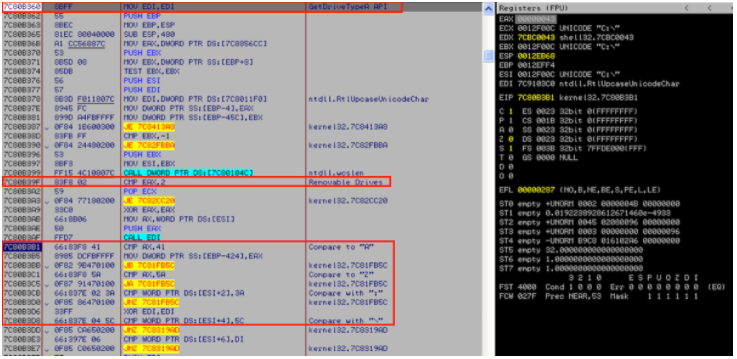
Jaff enumerates through the GetDrive API from letters A to Z for various types of local drives such as fixed, storage, and removable.
Jaff ransomware is designed to encrypt files even if the C2 check in fails. However, based on the most current assessment, Jaff ransomware sends a GET request to the Jaff domain ending in /a5 leading to the possible Snort signature:
alert any $HOME_NET any -> any any (msg:” possible Jaff C2 check-in alert”; content: flow:to_server,established; content:”GET”; “/a5/”; nocase; http_method; “pcre: “*(\/a5\/)$”; classtype: Trojan-activity)
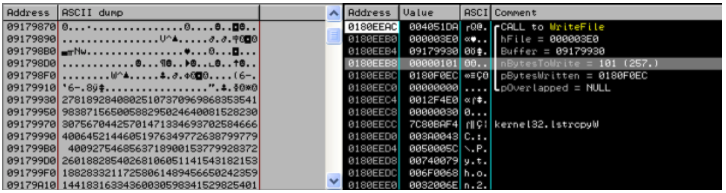
Based on analysis of the ransomware code, it is apparent Jaff uses both RSA and AES encryption algorithms using Windows Crypto API. The ransomware encrypts files by appending approximately 100 bytes to each file using a WriteFile Windows API call to each file fitting the target extension.
The Jaff ransomware is designed not to run under certain conditions. This mechanism can be imitated, leading to the creation of a mitigation strategy that can be used on machines before infection.
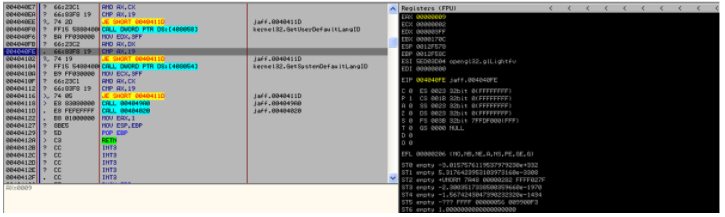
The API calls GetSystemDefaultLangID and GetUserDefaultLangID return 0x0409 in the EXTENDED ACUMULATOR REGISTER (EAX) on any US English-language machines. In this sense, 0x0409 is the locale culture identifier (LCID) for the English (United States) locale. However, the Jaff ransomware loads the return value into AX and compares it to the hardcoded value “19,” which is the AX identifier for the same calls if the language was set to Russian.
Below is the relevant disassembled routine that is used to check if the ransomware targets Russian-language machines:
call GetUserDefaultLangID
mov edx, 3ff
and ax, dx
cmp ax, 19
je .TerminateRansomwareProcess
call GetSystemDefaultLangID
mov edx, 3ff
and ax, dx
cmp ax, 19
je .TerminateRansomwareProcess

![Image 15: The Jaff ransomware targets various file extensions and deletes itself via a cmd[.]exe command.](https://www.flashpoint-intel.com/wp-content/uploads/2017/06/j15.png)
Additionally, when successfully launched, the Jaff ransomware uses a simple self-kill routine by executing the command “del /Q /F <path to Jaff ransomware>” via cmd[.]exe /c in order to delete the original ransomware executable from the victim machine.
The following file extensions are attacked by the Jaff ransomware:
.xlsx .acd .pdf .pfx .crt .der .cad .dwg .MPEG .rar .veg .zip .txt .jpg .doc .wbk .mdb .vcf .docx .ics .vsc .mdf .dsr .mdi .msg .xls .ppt .pps .obd .mpd .dot .xlt .pot .obt .htm .html .mix .pub .vsd .png .ico .rtf .odt .3dm .3ds .dxf .max .obj 7z .cbr .deb .gz .rpm .sitx .tar .tar .gz .zipx .aif .iff .m3u .m4a .mid .key .vib .stl .psd .ova .xmod .wda .prn .zpf .swm .xml .xlsm .par .tib .waw .001 .002 .003 . .004 .005 .006 .007 .008 .009 .010 .contact .dbx .jnt .mapimail .oab .ods .ppsm .pptm .prf .pst .wab .1cd .3g2 .7ZIP .accdb .aoi .asf .asp .aspx .asx .avi .bak .cer .cfg .class .config .css .csv .db .dds .fif .flv .idx .js .kwm .laccdb .idf .lit .mbx .md .mlb .mov .mp3 .mp4 .mpg .pages .php .pwm .rm .safe .sav .save .sql .srt .swf .thm .vob .wav .wma .wmv .xlsb .aac .ai .arw .c .cdr .cls .cpi .cpp .cs .db3 .docm .dotm .dotx .drw .dxb .eps .fla .flac .fxg .java .m .m4v .pcd .pct .pl .potm .potx .ppam .ppsx .ps .pspimage .r3d .rw2 .sldm .sldx .svg .tga .wps .xla .xlam .xlm .xltm .xltx .xlw .act .adp .al .bkp .blend .cdf .cdx .cgm .cr2 .dac .dbf .dcr .ddd .design .dtd .fdb .fff .fpx .h .iif .indd .jpeg .mos .nd .nsd .nsf .nsg .nsh .odc .odp .oil .pas .pat .pef .ptx .qbb .qbm .sas7bdat .say .st4 .st6 .stc .sxc .sxw .tlg .wad .xlk .aiff .bin .bmp .cmt .dat .dit .edb .flvv .gif .groups .hdd .hpp .log .m2ts .m4p .mkv .ndf .nvram .ogg .ost .pab .pdb .pif .qed .qcow .qcow2 .rvt .st7 .stm .vbox .vdi .vhd .vhdx .vmdk .vmsd .vmx .vmxf .3fr .3pr .ab4 .accde .accdt .ach .acr .adb .srw .st5 .st8 .std .sti .stw .stx .sxd .sxg .sxi .sxm .tex .wallet .wb2 .wpd .x11 .x3f .xis .ycbcra .qbw .qbx .qby .raf .rat .raw .rdb .rwl .rwz .s3db .sd0 .sda .sdf .sqlite .sqlite3 .sqlitedb .sr .srf .oth .otp .ots .ott .p12 .p7b .p7c .pdd .pem .plus_muhd .plc .pptx .psafe3 .py .qba .qbr .myd .ndd .nef .nk .nop .nrw .ns2 .ns3 .ns4 .nwb .nx2 .nxl .nyf .odb .odf .odg .odm .ord .otg .ibz .iiq .incpas .jpe .kc2 .kdbx .kdc .kpdx .lua .mdc .mef .mfw .mmw .mny .moneywell .mrw .des .dgc .djvu .dng .drf .dxg .eml .erbsql .erd .exf .ffd .fh .fhd .gray .grey .gry .hbk .ibank .ibd .cdr4 .cdr5 .cdr6 .cdrw .ce1 .ce2 .cib .craw .crw .csh .csl .db_journal .dc2 .dcs .ddoc .ddrw .ads .agdl .ait .apj .asm .awg .back .backup .backupdb .bank .bay .bdb .bgt .bik .bpw .cdr3 .as4 .tif .asp .hdr .iso.
Assessment
Flashpoint analysts continue to monitor the cybercriminal syndicate behind Jaff ransomware. These actors utilize the Necurs rootkit infections as a spam bot to deliver email spam with malicious attachments. Flashpoint assesses with moderate confidence that the threat actors who once favored Locky have now likely switched to using Jaff ransomware.
This Jaff syndicate remains one of the most active cybercriminal groups within the cybercrime landscape. Virtually every Russian-language cybercrime gang has an informal rule prohibiting the discussion of criminal activity directed against Russian nationals and other residents of the Commonwealth of Independent States (CIS) in order to avoid being targeted by Russian law enforcement. With the influx of press releases from Russian law enforcement about the arrest of major cybercrime gangs, security concerns remain a constant variable in the calculation of risk on the part of Russian-speaking cybercriminals. The Jaff actors also continue to avoid targeting any Russian-language victims via specific Windows API queries. This further supports the hypothesis that cybercriminals utilizing Jaff likely operate in a Russian-speaking country.
Mitigation
One possible Jaff ransomware mitigation strategy involves changing the machine’s language to Russian. One of the steps the ransomware takes is checking the language on the machine via the GetSystemDefaultLangID and GetUserDefaultLangID API. If Jaff detects that the language on the machine is set to Russian, it automatically terminates itself.
Organizations should continue to proactively collect indicators of compromise (IOCs) relevant to ongoing ransomware campaigns, as some variants, such as Jaff, continue to progress dynamically by leveraging discovered IOCs for counter-defensive procedures. As ransomware threats continue to evolve, it is crucial to develop and maintain good security hygiene, including robust patch and vulnerability management, data encryption, data backups, and vigorous user-access management controls.
Attachments & Downloads
To download the Jaff Ransomware indicators of compromise (IOCs), please click here.
Sources
https://www.flashpoint-intel.com/blog/necurs-dating-scam
https://www.cert.pl/en/news/single/necurs-hybrid-spam-botnet

