Blog
Inside a Twitter ‘Pornbot’ Campaign
Flashpoint analysts recently investigated the trend of adult entertainment-themed Twitter bots known as pornbots, which post tweets with hashtags containing popular brand names alongside random, unrelated terms. The observed set of pornbots appears to be a mix of compromised accounts and accounts specifically created to advertise pornography. As such, organizations mentioned in these bots’ pornographic advertising campaigns on Twitter may suffer reputational damage in addition to distorted social media engagement campaign metrics.

Flashpoint analysts recently investigated the trend of adult entertainment-themed Twitter bots known as pornbots, which post tweets with hashtags containing popular brand names alongside random, unrelated terms. The observed set of pornbots appears to be a mix of compromised accounts and accounts specifically created to advertise pornography. As such, organizations mentioned in these bots’ pornographic advertising campaigns on Twitter may suffer reputational damage in addition to distorted social media engagement campaign metrics.

In recent years, Twitter has become a primary form of external, two-way communication and engagement for organizations across all sectors. For example, companies often use hashtags to monitor the spread and reception of marketing campaigns and sponsored events. More crucially, emergency services may use hashtag tracking to gain real-time insight into current situations during natural disasters and other crises. In a worst-case scenario, pornbots or other spambots could identify a trending hashtag and distort the conversation by sharing unrelated or false information.

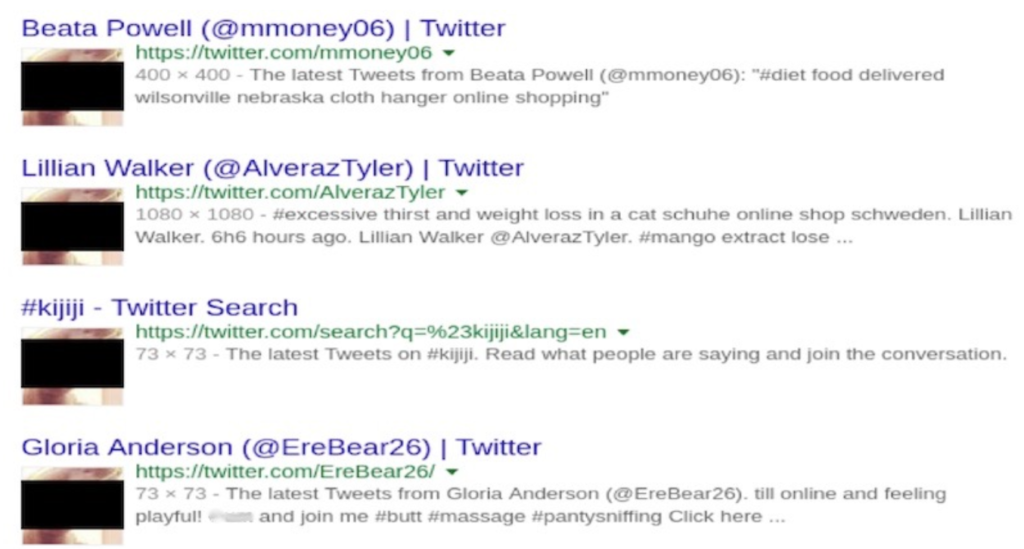
Flashpoint analysts identified three distinct sets of pornbots using identical hashtags, indicating they were likely part of the same organized campaign. While similar in appearance and often using a common set of profile pictures across the groups, each promoted a different adult website. However, the three adult websites linked to the sample profiles shown above were hosted on one of two common servers, which may indicate the pornbots share a common origin. Flashpoint analysts did not detect any malicious files on the servers hosting the websites advertised by the pornbots.
Advertising Methods
Flashpoint analysts observed two primary methods of advertising across the pornbot accounts:
• Hashtagged tweets: The first advertising method utilized hashtags followed by random risqué buzzwords and a link to an adult dating or video website, often featuring online “cam girls” or escort services.
• Link in bio and pinned tweet: The second advertising method includes multiple accounts sharing similar bios and pinned tweets, which contain links to adult content sites.


Identifying Pornbots

Over the course of their investigation, Flashpoint analysts noted several common traits that can be used to identify pornbots and other spambots:
• Reused profile images: The profile pictures used by the observed pornbots were all obtained from public profiles on open-source websites, primarily Instagram and Pinterest. Reverse searches using Google Images indicated these stolen images were resused by multiple pornbots.
• Systematic coordination: Related sets of pornbots systematically coordinated their tweets. One pornbot would post a tweet containing a hashtag, and other pornbots within its group would subsequently post tweets containing the same hashtag, followed by random and unrelated terms.
• Many tweets, but few followers: Each of the observed pornbots posted tweets at a rapid cadence, with some posting more than 50 times per day. Most of the observed pornbot accounts boasted more than 10,000 tweets, but typically had fewer than 200 followers. Similarly, most of the pornbots were following fewer than 200 other users.

Pornbot Mitigation Best Practices
The following mitigation measures may help reduce the number of pornbots and spambots using brand names. These steps may also reduce the number of false detections and aid in validating social media metrics:
• Challenge social media teams to identify and block pornbots and spambots following company social media accounts. This action impacts the bots’ ability to capture and retweet relevant and branded tweets.
• Require social media teams to report these accounts through Twitter’s abuse function.
• Implement response actions to react to large campaigns, such as social media teams and cyber threat teams notifying each other when activity is detected.

