Blog
Facing Five Types of Ransomware and Cyber Extortion
With every passing day, ransomware operators and cyber extortion syndicates grow increasingly emboldened. Look no further than to the recent DarkSide ransomware attack that effectively took down Colonial Pipeline systems and its 5,500 miles of gas supply lines for close to a week. Historically, ransomware groups targeted smaller organizations and those with less mature security programs. But their ambitions have expanded dramatically in recent years, setting their sights on increasingly larger organizations with more lucrative ransom returns.

Specialized Ransomware and Cyber Extortion on the Rise
With every passing day, ransomware operators and cyber extortion syndicates grow increasingly emboldened. Look no further than to the recent DarkSide ransomware attack that effectively took down Colonial Pipeline systems and its 5,500 miles of gas supply lines for close to a week. Historically, ransomware groups targeted smaller organizations and those with less mature security programs. But their ambitions have expanded dramatically in recent years, setting their sights on increasingly larger organizations with more lucrative ransom returns.
“The novel fact is 10% of breaches now involve ransomware.”
—2021 Verizon DBIR
At the same time, extortion and ransomware groups continue to mature themselves. Not only do they improve their attack tools, techniques, and procedures (TTPs), but also other components of their operations advance, like adding well-run marketing and public relations functions.
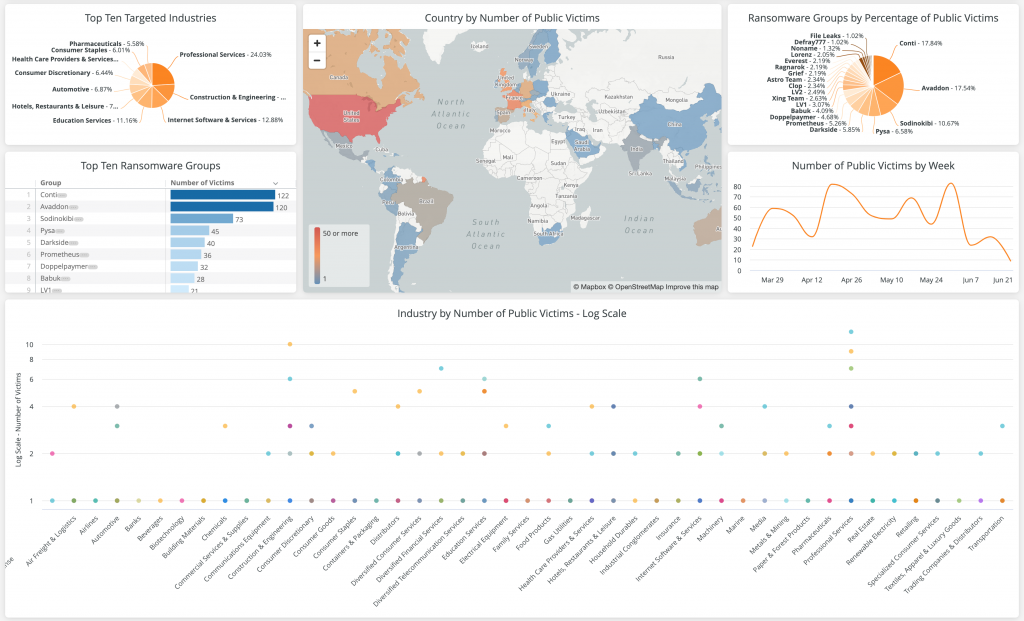
10 Ransomware Groups Add Nearly Six New Victims Every Day
Each successful extortion campaign further incentivizes cybercriminals to pursue new attacks and form new extortion gangs to coordinate and carry out their attacks. In the past 90 days alone, the 10 most active ransomware groups amassed a total of 535 new victim postings, according to Flashpoint threat data. In other words, these 10 groups alone executed an average of 5.94 successful ransomware attacks per day over the last 90 days—at a minimum.
Why at a minimum? Because this data only accounts for the victim organizations that ransomware groups list and shame publicly from their ransomware sites. Many more victim organizations negotiate their omissions from these ransomware shame lists as a condition of their ransomware payment.

If at First Ransomware Doesn’t Succeed, Try, Try Again (with Other Cyber Extortion Methods)
Even though ransomware has become a tried and true tactic, it doesn’t always work. For some organizations, the threat of extended operational downtime is not as worrisome as it is to many others. In other cases, organizations have robust backup and recovery contingency plans, minimizing the downtime of any successful attack.
Unfortunately for these better-prepared organizations, however, ransomware is only one tool in the expanding cybercriminal extortion toolkit. Cybercriminals increasingly pursue multi-pronged ransomware attacks that add contingency extortion methods (e.g., threaten to publicly release sensitive or strategic data captured as part of the initial attack) should the threat of encryption lockout and downtime fail to appropriately intimidate the intended target.
Today, Flashpoint sees five types of ransomware and cyber extortion—which organizations often face more than one at a time. We explore these types and their effects in the following sections below.
1) Corporate Doxxing and Victim Shaming Sites
Once a novelty, ransomware websites that publicly shame and expose sensitive data of the new, non-paying victims are now the norm. Ransomware groups—including Clop, Conti, and many others—regularly list new ransomware victims on their websites in an effort to receive payment. Starting with a simple post of the organization’s name, and often a small amount of sample data to prove the breach is legitimate, these groups gradually release more and more information until a victim either pays, or all of the data is released, as seen below with DoppelPaymer’s site.
The data released in these dumps may vary, but in many cases, they attempt to reveal information such as third party data, PII, financial information, and potentially even access information like credentials. Information leaked in these breaches may help other attackers or cyber criminals further target a victim.

2) Data Sell-Off Auctions
Depending on the type and expected financial value of the data stolen during the initial attacks, ransomware groups may choose alternate methods to ensure they maximize their returns. Data sell-off auctions are one such option that ensures the data stolen during the ransomware attack isn’t left un-monetized.
Rather than negotiating with only one victim buyer, ransomware groups open up the bidding to all interested buyers by holding public, online auctions to sell off various portions of the data to highest bidders. One of the first ransomware groups to pilot this approach was Sodinokibi (aka “REvil”), known for a few of their sell-off ransomware auctions after amassing stolen data associated with high-profile celebrities, like Lady Gaga, Madonna, and Trump.
These sell-off auctions introduce new and higher degrees of risk. While general data dumps certainly expose victim organizations, they’re likely to get commoditized quickly as the data acts as the fuel of high-volume automated attacks (e.g., credential stuffing). With sell-off auctions, organizations lose both business-critical information and are at higher-risk of more sophisticated and strategic attacks since their data remains semi-private, exclusively for the cybercriminal purchaser to use at their sole discretion.
Learn more about Flashpoint Threat Response and Readiness to prepare and manage your response to ransomware attacks whenever they strike.
3) Multistage Cyber Extortion with DDoS Attacks
Distributed denial-of-service (DDoS) attacks add layers of confusion and complexity to ransomware attacks, typically as an additional attack tactic on top of the standard ransomware file encryption. Organizations that might otherwise focus all attention on the ransomware attacks themselves, now face the added burden of simultaneously addressing system lockouts from the ransomware alongside with worsening network and system uptimes stemming from the DDoS attacks.
Knowing the enhanced stress DDoS attacks add to DDoS attacks, certain ransomware groups—including Sodinokibi, SunCrypt, and RagnarLocker—increasingly launch these multi-stage ransomware and DDoS attacks against their targets. Even after systems are restored, these combined attacks often leave victim organizations scrambling to restore full system functionality and address frustrated customers.
4) Media Amplification and Cold Calling
If initial ransomware attacks aren’t menacing enough to coax victim organizations into paying out their ransoms, then ransomware groups turn to techniques that further ratchet up the heat on the victim organization. In particular, groups like Sodinokibi, Conti, and Ryuk, take to VOIP cold calling to connect with high-profile journalists and media outlets that may cover the breach in the news. Cybercriminals may also reach out to other concerned stakeholders, such as the victim’s third-party vendors, suppliers, and strategic business partners—all of whom may be affected and may question why they’re hearing the news first from ransomware groups instead of their trusted partner.
5) Customer Calls to Action
Lastly, ransomware groups even attempt to contact the victim organization’s own clients and customers to apply pressure and push the victim into action. In a recent breach by the now-defunct ransomware group, Cl0p, the ransomware collective used some of the customer contact information that it stole as a part of the ransomware attack to reach out to the customers directly and urge the victim organization to pay the ransom to ensure their personal and account data remained secure.
Turn Threat Intelligence into Threat Mitigation
As ransomware and other cyber extortion threats continue to escalate, so too do the mitigation capabilities that organizations have at their disposal to minimize the impact of ransomware attacks and, in some cases, even avert them altogether. Flashpoint Threat Response and Readiness solutions offer organizations ways to reinforce and simulate their preparations, along with leveraging advanced analytics, automation, and industry-leading technical collections, organizations can stay on top of their threat environments, continuously assess their ransomware risk postures, and take immediate and informed action whenever new attacks emerge.
Track Evolving Cyber Extortion Activity with the Flashpoint Ransomware Dashboard
Prepare for Ransomware and Cyber Extortion with Flashpoint
Request a demo and see firsthand how Flashpoint’s Threat Response and Readiness offerings ensure your entire team is prepped and able to respond to any ransomware attack. When equipped with Flashpoint’s dedicated ransomware dashboards, you move ahead of ransomware and the cybercriminal groups who deploy it.