Blog
Cybercriminal Abuse of Rewards Points
Cybercriminal interest in stolen data is not solely limited to financial or personally identifiable information. In fact, Flashpoint analysts have observed Deep & Dark Web chatter pertaining to the exploitation of rewards points programs, especially those associated with travel. This chatter aligns with cybercriminals’ interest in fraudulent booking services for hotels, airline tickets, and car rentals—all of which have proliferated in various underground communities over the past several years.

Cybercriminal interest in stolen data is not solely limited to financial or personally identifiable information. In fact, Flashpoint analysts have observed Deep & Dark Web chatter pertaining to the exploitation of rewards points programs, especially those associated with travel. This chatter aligns with cybercriminals’ interest in fraudulent booking services for hotels, airline tickets, and car rentals—all of which have proliferated in various underground communities over the past several years.
Actors who offer these illicit “booking services” first obtain access to various types of travel rewards points. This typically occurs via compromised user accounts—particularly those associated with rewards points credit cards. Actors then use these points to purchase hotel rooms, flights, and car rentals through online booking services.
These services have become so widespread on one lower-tier Russian-language forum that the community has established its own group of members dedicated to cybercrime targeting hotels. One such member has been advertising their travel “booking service” on two lower-tier forums since December 2014. Through their service, users can order tickets to anywhere in the world; the only restriction is no domestic flights within Russia. Grateful customers regularly post photos taken on trips purchased through the actor’s offerings.

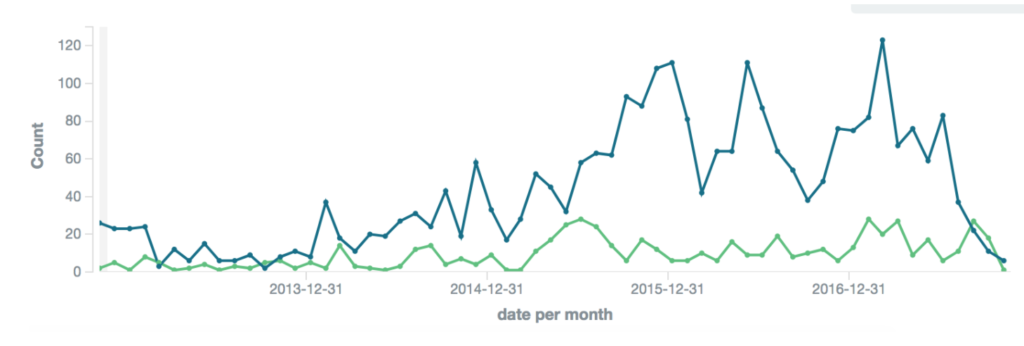
Beyond the Russian-language underground, rewards points abuse also occurs among English and Spanish-speaking cybercriminals. Similar Illicit booking services had been listed on the now-defunct AlphaBay Market since at least March 2015. These listings drove high demand—3,601 customers purchased one actor’s illicit hotel and car rental services between March 2015 and December 2016. To cash in on this trend, at least one vendor who was active on lower-tier Russian-language forums is known to have expanded their operations to AlphaBay Market in September 2016.
Today, similar services are available on various other English-language marketplaces.
Although now-defunct, the most prolific rewards point fraud service on the Spanish-language underground was an illicit “travel agency” that offered discounted tickets and reservations for flights, five-star hotels, car rentals, cruises, and other vacation activities such as tours. Clients were allowed and even encouraged to make these reservations in their own names, and reservations were able to be made anywhere from a month to only hours in advance. Much like the aforementioned Russian-language vendor, this Spanish-language “agency” would not book any domestic flights, stating that there was little money to be made there. Moreover, they would only book hotel reservations if the total cost was to be more than $200 USD. Interestingly, their prices were largely based on comparable hotel room listings advertised on surface web travel sites.
It should be noted that travel arrangements aren’t the only illicit use of stolen rewards points, which can often be used to purchase gift cards. One actor on AlphaBay Market was observed selling $100 USD gift cards for various retail and restaurant chains.
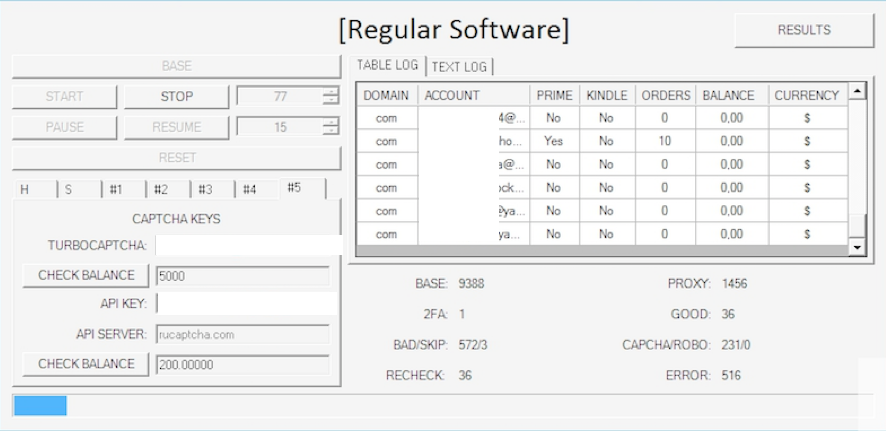
Cybercriminal abuse of rewards points has also been facilitated by the development of brute forcing software, which can be used to systematically check a large number of possible password combinations until the correct one is determined. After obtaining a user’s password through brute forcing, cybercriminals can potentially access any rewards points associated with the compromised accounts. A symbiotic relationship exists between the expanding presence of these tools and the marketplace for compromised credentials.
Flashpoint analysts assess with a moderate degree of confidence that rewards points abuse will likely continue. That being said, businesses and everyday consumers alike can reduce the likelihood of their rewards points being stolen by practicing stringent password hygiene. Since brute forcing tools often used to access rewards points automatically test countless combinations of characters with the goal of identifying and entering the correct password, the difficulty of guessing a password increases exponentially along with its character length and complexity.
