Blog
The Curious Case of the flokibot Connector Malware
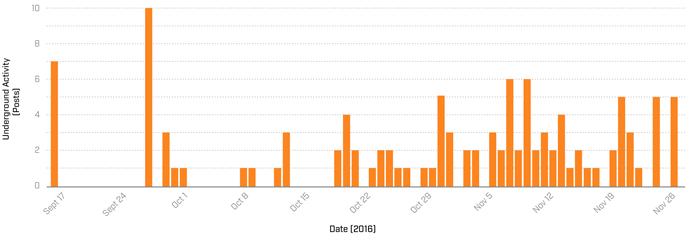
In the financial cybercrime landscape, we see a continuous progression of the malware known as “Floki Bot,” which has been marketed by the actor “flokibot” since September 2016

KEY TAKEAWAYs
• In the financial cybercrime landscape, we see a continuous progression of the malware known as “Floki Bot,” which has been marketed by the actor “flokibot” since September 2016.
• Language is not a barrier: though experience suggests that many cybercriminals tend to stay within their language groups, those with a high level of motivation (like flokibot) can use online language tools to participate in foreign online communities nearly as effectively as native speakers.
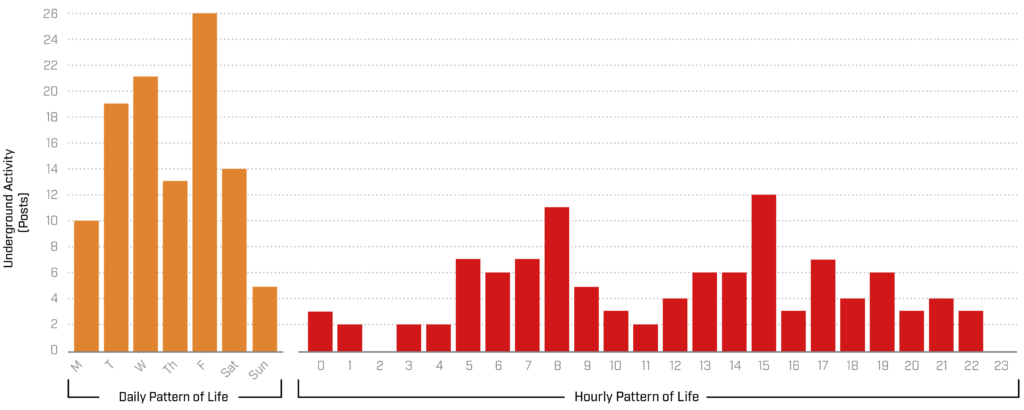
• Cybercriminals learn quickly: flokibot’s introduction to and participation in illicit activity did not take place over many years. Within as short a time as two months, flokibot was able to hold their own with seasoned cybercriminals, becoming an embedded member of their communities.
• With the leaked ZeuS source code and the multiplication of tutorials and other learning materials in cybercrime communities, the time required to attain a high level of skill and sophistication has been continuously reduced.
• As criminals share information to defeat protections, we should be sharing it as well with our community to defeat threats.
• Our joint partnership with Cisco Talos facilitated a proactive approach to mitigation and disruption of the threat, leveraging our technical and intelligence capabilities. While Talos developed early signature detection that allows early identification and mitigation of this threat, Flashpoint provided actor and campaign intelligence observed from the Deep & Dark Web.
Background
A few months ago, Flashpoint analysts became interested in a Brazilian actor who uses the pseudonym “flokibot.” This actor is remarkable for a number of reasons, in particular their presence in a number of top-tier underground communities across a range of languages. The actor is perhaps most interesting, however, because of their activity in the development and maturing of a Trojan known as “Floki Bot,” which was offered for $1,000 USD in Bitcoins. By obtaining intelligence from the Deep & Dark Web (DDW) and in coordination with Talos, Flashpoint monitored malware campaigns associated with flokibot.
In this report, we detail recent Flashpoint research related to the Brazilian “connector,” flokibot. The term “connector” is used to describe the overlap between criminal communities across disparate language forums. Connectors are individuals who interact on forums that are maintained outside of their country of residence and import knowledge and tools into their native communities.
While criminal actors continue to communicate through a number of mediums, including social media, IRC, and Telegram, this report focuses on analysis of the campaigns and social networks of this Portuguese-speaking actor on the DDW. Specifically, flokibot reaches across language barriers into communities in which the dominant language is English or Russian.
Floki Bot Progression on the Deep & Dark Web
Malware developers continually adapt their technology to bypass detection and controls. These new malware strains are often developed by actors operating in the DDW before being released into the wild without forewarning, leaving companies flat-footed and reactive.
In our previous blog entitled “Multi-Purpose “Floki Bot” Emerges as New Malware Kit”, we noted that this malware is based on publicly-available ZeuS 2.0.8.9 source code, to which flokibot has made several notable modifications. Besides the dropper method, Floki Bot also employs a different network protocol than ZeuS that allows it to avoid detection by Deep Packet Inspection (DPI).
Brazilian Actor-Connector flokibot
Beyond the unique intelligence obtained by Flashpoint analysts and the campaign targeting Brazil, flokibot, a Portuguese-speaking member of English and Russian-language communities, was identified by several markers as very likely to be Brazilian:
• Use of the Portuguese language within the actor’s communications
• Targeting computers with the default language set to Portuguese
• Targeting Brazilian domains or IP ranges
• Targeting computers with the default timezone set to Brazil UTC -03:00
• Other unique intelligence obtained by Flashpoint analysts
Brazil-Russian Underground Cooperation: Case of flokibot
The phenomenon of connectors has been readily apparent in English and Russian-language communities, wherein Portuguese-speaking actors have likewise maintained a presence in order to learn and strengthen their technical skills and criminal targeting.
While Brazilian cybercriminals are not typically as technically sophisticated as their Russian counterparts, they will often solicit new forms of malware (to include point of sale [PoS] ransomware and banking Trojans), or offer their own services. It appears that a presence on Russian DDW communities may be a likely factor in flokibot’s progression.
PoS Malware: Technical Competency
For connectors like flokibot, reaching across language barriers into predominantly English- and Russian-language communities enables them to to advance criminal schemes through new markets: it is not particularly difficult or expensive for botnet newcomers in short time to build their own botnets leveraging Floki Bot and start attacking corporate networks.
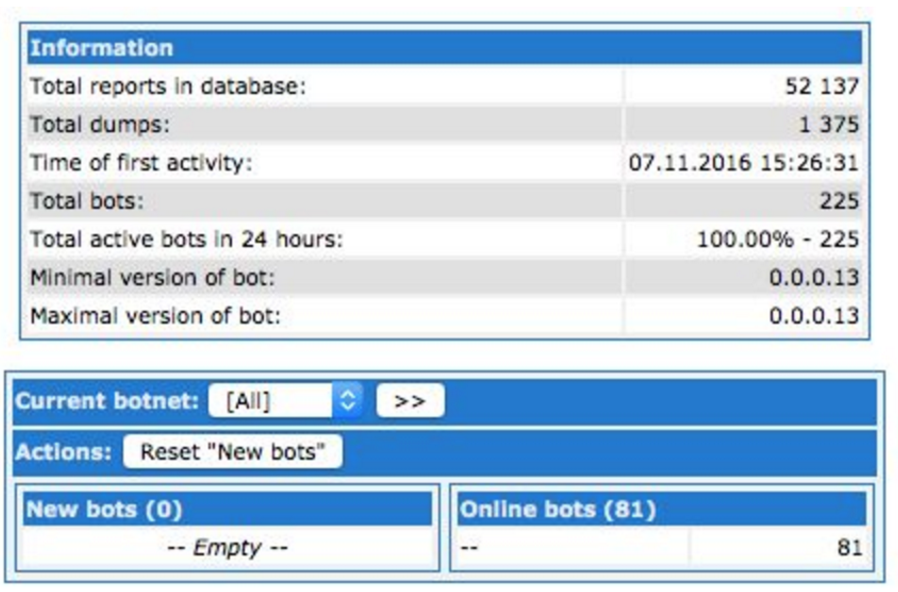
One way in which flokibot’s technical competency has evolved is in the actor’s use of hooking methods to capture track data from PoS devices. While the malware originates from the well-known ZeuS 2.0.8.9 source code, flokibot adds this hooking method to grab track data from memory thereby extending the malware operations beyond regular banking trojan functionality making it more potent and versatile.

